Using PowerShell Empire with a Trusted Certificate
Carrie Roberts* // Using a trusted certificate and non-default Empire options will help increase your chances of getting a successful session out of a network. Follow these instructions to get […]
Carrie Roberts* // Using a trusted certificate and non-default Empire options will help increase your chances of getting a successful session out of a network. Follow these instructions to get […]
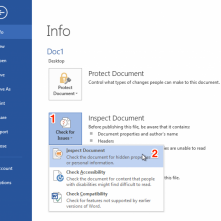
Ethan Robish // In my last two posts I showed how to insert tracking bugs in both .docx (Part 1) and .xlsx files (Part 2). But don’t let all that effort go […]
Carrie Roberts // Tired of typing those Empire commands to startup your goto listeners? Wish there was an equivalent to Metasploit resource files for Empire? This is not currently […]

Logan Lembke // Step One: Power. Step Two: Enter. Step Three: ???? Step Four: Profit. In the security industry, we love our encryption. However sometimes, the complexity introduced by encryption […]

Jordan Drysdale // … Alternate Title: “Why I Love BHIS” So, I was gifted this cute little princessy-toy thing recently. My first thought was that my daughters will love this thing. […]
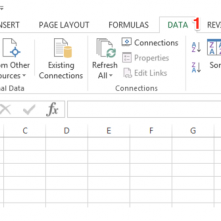
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]
Carrie Roberts // There are various reasons why having a webDAV server comes in handy. The main reason I created one was to execute a malicious Outlook rule attack as […]

Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]

Beau Bullock // Full Disclosure: Black Hills Information Security believes in responsible disclosure of vulnerabilities. This vulnerability was reported to Microsoft on September 28th, 2016. As of the publication date of […]